200 Vendors. 6 Dimensions. 2 Seconds: Real-Time Vendor Risk Intelligence
Table of Contents
Your vendor risk team has a backlog of 200+ vendors awaiting assessment. Each manual evaluation takes 40–80 analyst hours and costs $3,600–$8,000. Federal SBOM mandates and NIS2 supply chain requirements are accelerating the timeline. And the board wants a defensible vendor risk posture by next quarter. This is the story of how a VP of Vendor Risk uses ComplianceHarbor’s 48 MCP tools—including internal control connectors and automated remediation workflows—to assess an entire vendor pipeline in the time it used to take to evaluate one.
1. The Business Problem
Third-party risk has become the fastest-growing attack surface in enterprise security. According to the Ponemon Institute, 59% of organizations experienced a data breach caused by a third party or supplier in the past 12 months. Yet the tools available for vendor risk assessment remain stuck in the spreadsheet era.
Consider the math facing a typical VP of Vendor Risk:
- $3,600–$8,000 per manual assessment: Security questionnaires, SOC 2 report reviews, penetration test analysis, and compliance mapping for a single vendor consume 40–80 analyst hours at $90–$100/hr
- 200+ vendor backlog: New SaaS onboarding, contract renewals, and M&A due diligence create a perpetual queue that grows faster than the team can process
- Federal SBOM mandates: Executive Order 14028 requires software bill of materials for federal suppliers, and NIS2 extends supply chain security obligations across the EU—both with enforcement deadlines your vendors may not be ready for
- Point-in-time blindness: Even when a vendor is assessed, the evaluation reflects a snapshot. Security posture degrades continuously between annual reviews—and that is exactly when breaches happen
The cost of getting this wrong is not theoretical. The SolarWinds breach, the MOVEit exploitation, and the Log4Shell supply chain cascade all demonstrated that vendor risk failures propagate at machine speed through interconnected systems. Manual, periodic assessments cannot defend against threats that operate continuously. ComplianceHarbor’s 48 MCP tools provide continuous, real-time vendor risk intelligence with internal control signal enrichment and automated remediation tracking.
2. The Demo Walkthrough
Step 1: Assess Vendor Risk — 6-Dimension Breakdown
The assess_vendor_risk tool evaluates a vendor across six risk dimensions simultaneously, drawing from real-time external intelligence sources. A single API call returns a comprehensive risk profile in under 2 seconds:
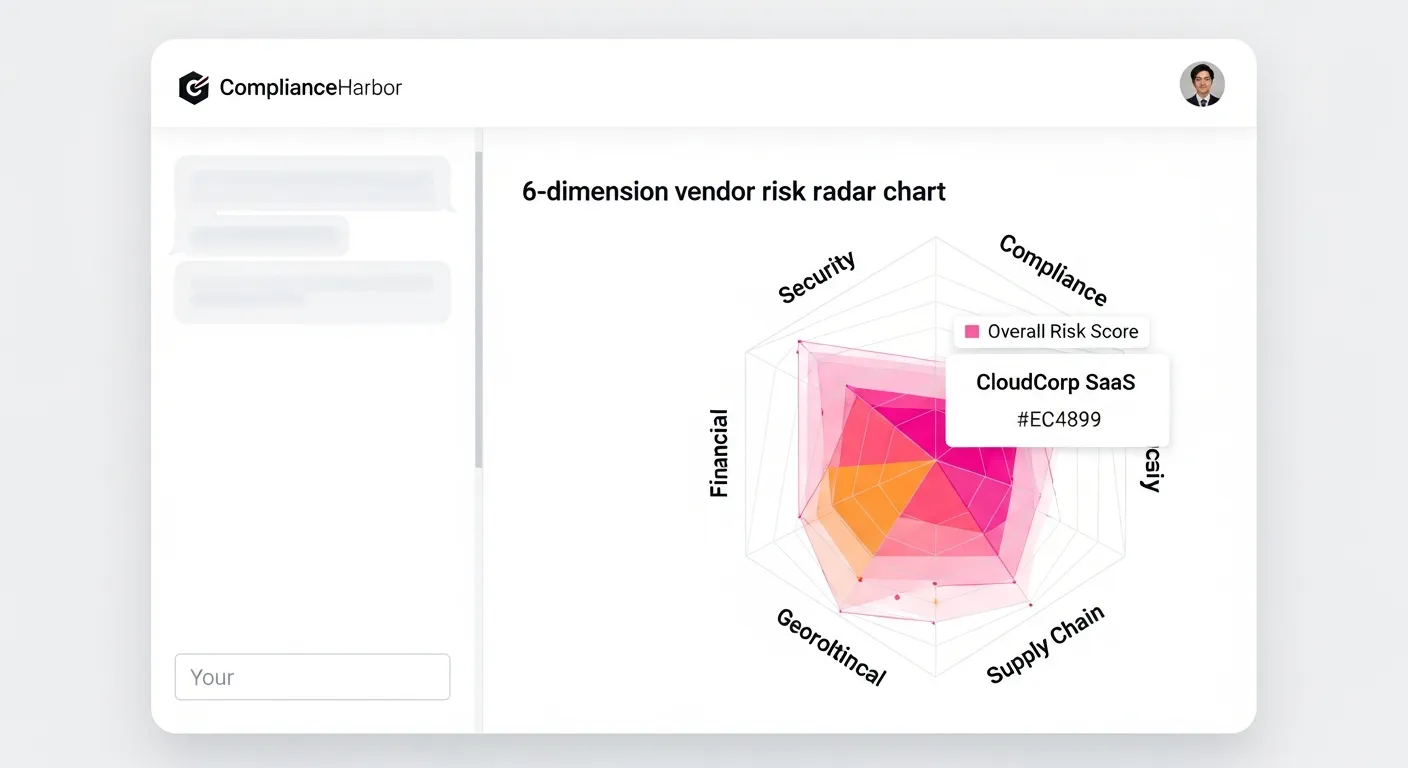
Each of the six dimensions provides a scored, evidence-backed evaluation:
- Vulnerability Exposure: Queries NVD and CISA KEV for active CVEs affecting the vendor’s disclosed technology stack, weighted by CVSS severity and exploit availability
- Security Rating: Aggregates external security posture signals including DNS configuration, TLS certificate health, email authentication (SPF/DKIM/DMARC), and open port exposure
- Incident History: Cross-references dark web intelligence feeds and breach databases for historical compromise indicators tied to the vendor’s domain and infrastructure
- Operational Health: Evaluates the vendor’s cloud provider dependencies, uptime track record, and infrastructure resilience signals
- Compliance Posture: Checks for active certifications (SOC 2, ISO 27001, FedRAMP), regulatory alignment, and compliance calendar adherence
- EOL Exposure: Identifies end-of-life or end-of-support software in the vendor’s stack that will no longer receive security patches
The composite score drives an automated tier classification—Critical, High, Medium, or Low risk—with a narrative rationale explaining the primary risk drivers.
Step 2: Supply Chain Risk & Dark Web Exposure
Beyond the primary risk dimensions, ComplianceHarbor enriches the vendor profile with targeted intelligence checks:
check_supply_chain_risk: Evaluates the vendor’s upstream dependencies, concentration risk from shared infrastructure providers, and SBOM completeness against federal mandate requirementscheck_dark_web_exposure: Scans dark web intelligence feeds for leaked credentials, breach data, and threat actor interest associated with the vendor’s domains and infrastructurecheck_vendor_security_rating: Provides a letter-grade security rating (A–F) based on externally observable security posture indicators, comparable to financial credit ratings for cybersecuritycheck_domain_health: Validates DNS configuration, TLS certificate chain integrity, certificate transparency log monitoring, and domain reputation signals
Each of these checks runs in parallel, contributing scored inputs to the composite vendor risk profile. The result is a vendor assessment that would take a human analyst 40–80 hours—completed in under 2 seconds with full evidence chain.
Step 3: Batch Assessment — 5 Vendors Simultaneously
The real power emerges at scale. The batch_assess tool processes multiple vendors in parallel, identifying cross-vendor risk patterns and shared infrastructure dependencies that individual assessments would miss:
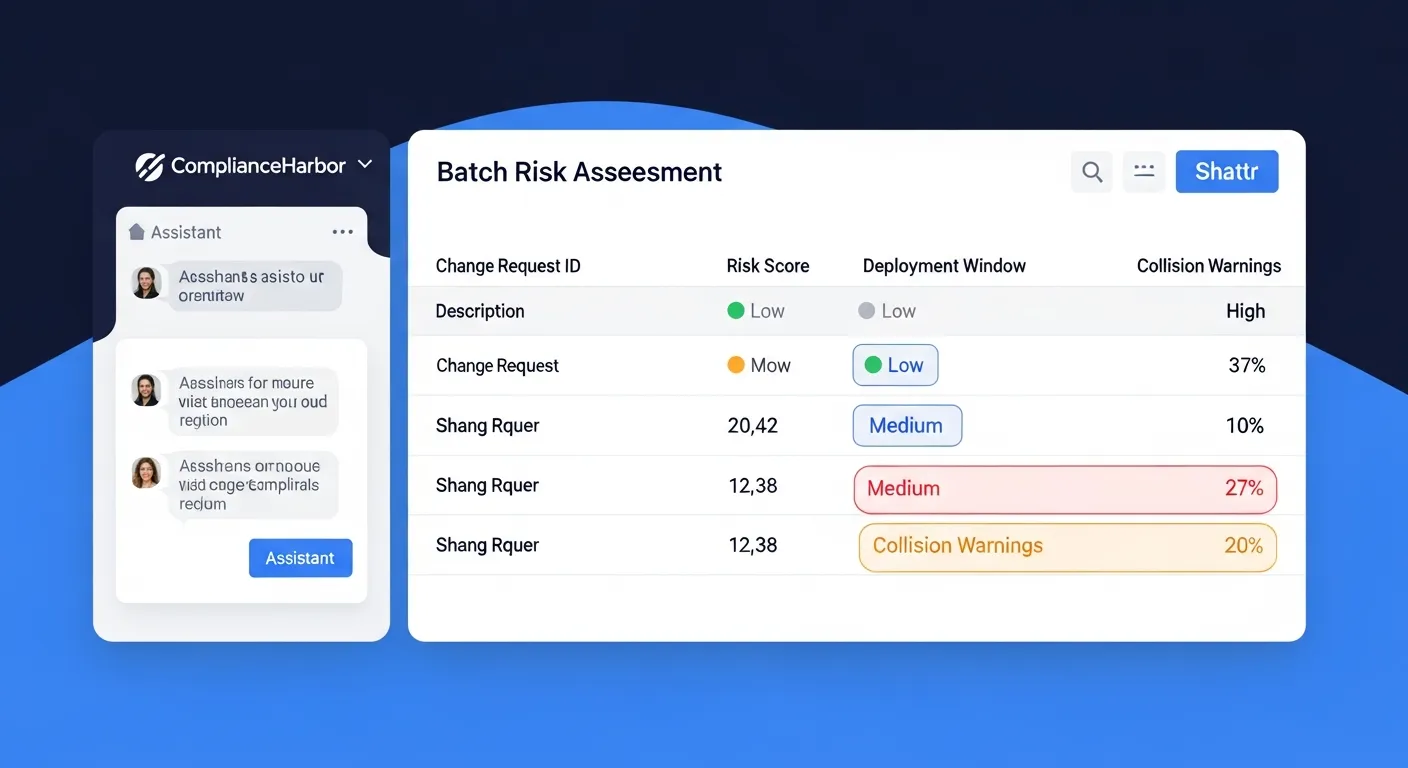
The batch assessment reveals patterns invisible to sequential evaluation:
- CI Overlap Warnings: Two vendors sharing the same cloud infrastructure provider means a single provider outage could cascade across multiple critical business functions simultaneously
- Concentration Risk: When 60% of your vendor portfolio depends on the same three upstream providers, your actual risk exposure is dramatically higher than individual vendor scores suggest
- Comparative Scoring: Color-coded risk levels across all vendors enable instant prioritization of which relationships require immediate remediation versus routine monitoring
Step 4: Enrich Vendor Risk with Internal Control Connector Signals
ComplianceHarbor’s Internal Control Connectors add a powerful internal dimension to vendor risk assessment. By ingesting signals from your own identity, endpoint, and ticketing systems, the platform cross-references your internal security posture against vendor access patterns:
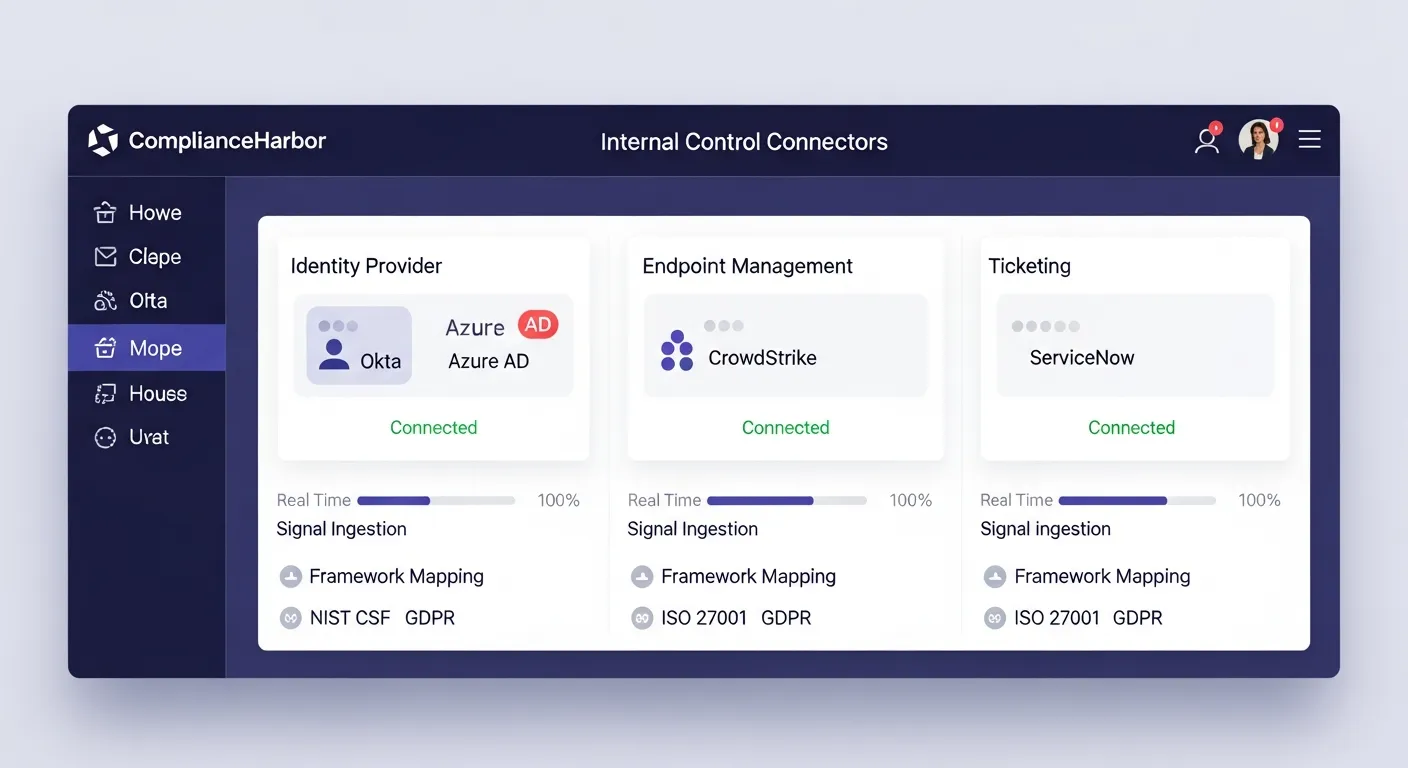
- Identity Signals (Okta/Azure AD): MFA enrollment rates, access review status, and privileged account usage for vendor-connected service accounts—mapped to SOC 2 CC6.1 and NIST CSF PR.AC-1
- Endpoint Signals (CrowdStrike/Defender): EDR coverage, patch compliance, and detection rates on systems that interact with vendor APIs and data—mapped to NIST CSF DE.CM-08 and SOC 2 CC7.1
- Ticketing Signals (ServiceNow/Jira): Open vendor-related incidents, SLA compliance, and change approval rates—mapped to ITIL 4 and SOC 2 CC8.1
These internal signals create a bidirectional risk view: not just how risky the vendor is, but how well your own controls protect against vendor-related exposure. A vendor with a medium external risk score but weak internal controls around their access becomes a high-priority remediation target.
Step 5: Auto-Create Remediation Findings for High-Risk Vendors
Vendors that exceed risk thresholds automatically generate tracked remediation findings via the create_remediation_findings tool. Each finding tracks the specific risk drivers—whether from external intelligence or internal control gaps—through a full remediation lifecycle:
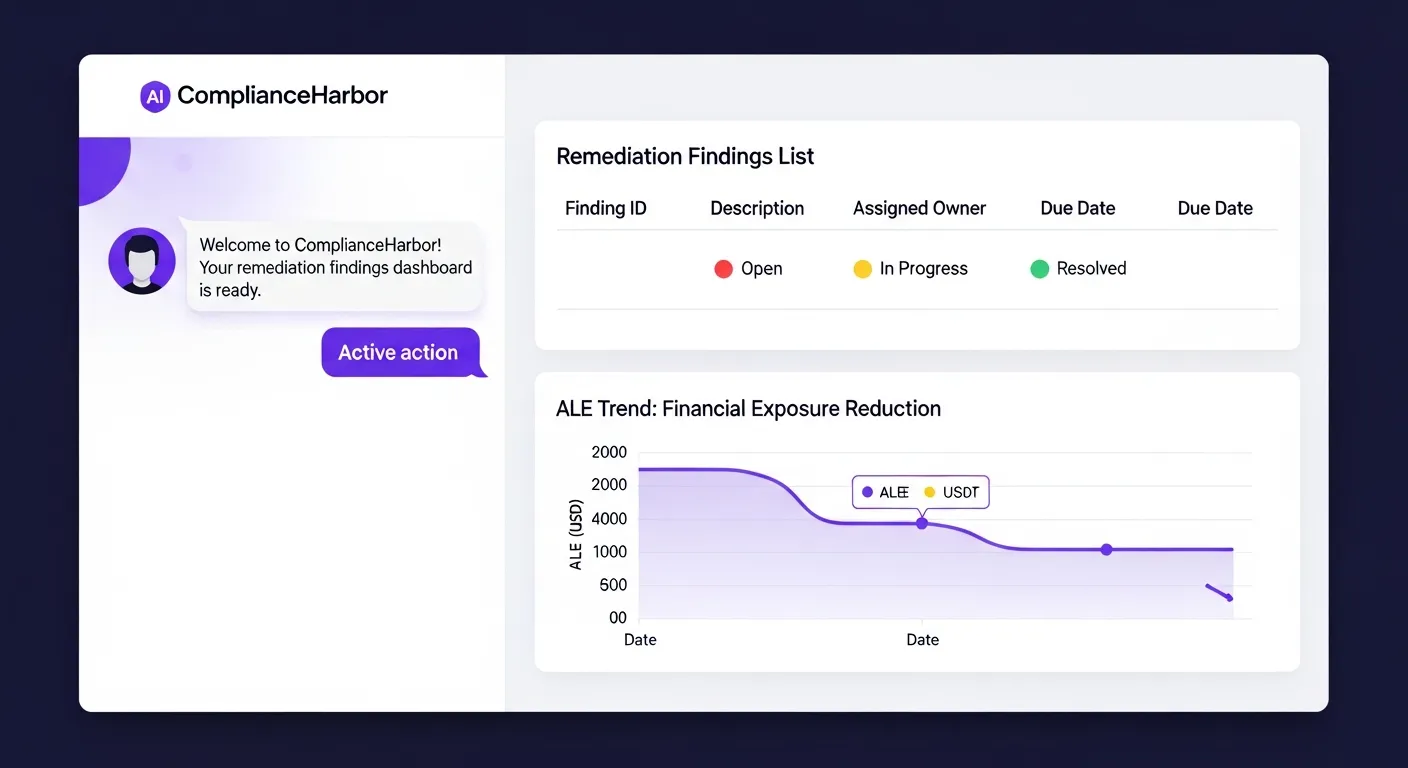
- Status Lifecycle: Each vendor risk finding progresses through open → in_progress → resolved/accepted, with full audit trail at each transition
- ALE Trend Tracking: Annualized Loss Expectancy charts quantify the financial impact of unresolved vendor risk over time
- SHA-256 Evidence Receipts: When a vendor risk finding is resolved—through vendor remediation, compensating controls, or risk acceptance—a cryptographically signed evidence receipt is generated
- Vendor Renewal Linkage: Open remediation findings automatically surface during vendor contract renewal assessments, ensuring unresolved risks are addressed before renewals are approved
3. Tools Included in VendorRisk
| MCP Tool | What It Returns |
|---|---|
| assess_vendor_risk | 6-dimension risk scorecard with composite score, tier classification, and narrative rationale |
| check_supply_chain_risk | Upstream dependency analysis, concentration risk, SBOM compliance status |
| check_dark_web_exposure | Leaked credentials count, breach history, threat actor mentions, exposure severity |
| check_vendor_security_rating | Letter-grade security rating (A–F) with sub-scores for network, application, DNS, and email security |
| check_domain_health | DNS configuration, TLS certificate validity, certificate transparency monitoring, domain reputation |
| batch_assess | Parallel multi-vendor assessment with cross-vendor overlap warnings and concentration analysis |
| check_certificate_intelligence | Shadow certificates, wildcard abuse, burst issuance, CA diversity analysis for vendor domains |
| map_attack_surface | TTP-to-CVE attack surface mapping with known threat actors for vendor technology stacks |
| ingest_identity_signals | MFA enrollment, access review status, and privileged account metrics from Okta/Azure AD (SOC 2 CC6.1) |
| ingest_endpoint_signals | EDR coverage, patch compliance, and detection rates from CrowdStrike/Defender (NIST CSF DE.CM-08) |
| ingest_ticketing_signals | Open incidents, SLA compliance, and change approval rates from ServiceNow/Jira (SOC 2 CC8.1) |
| create_remediation_findings | Tracked remediation findings from high-risk vendor assessments with ALE trend data |
| list_remediation_findings | Filtered list of vendor risk findings by status, severity, or vendor |
| resolve_remediation_finding | SHA-256 evidence receipt confirming vendor risk finding resolution |
4. Sample API Response
The assess_vendor_risk tool returns a structured JSON response containing the full 6-dimension risk profile. Here is the response shape your consuming application receives:
{
"vendor": "CloudCorp SaaS",
"overall_risk_score": 45,
"risk_tier": "medium",
"risk_dimensions": {
"vulnerability_exposure": {
"score": 16,
"cves_found": 7,
"critical_cves": 1,
"max_cvss": 9.8,
"detail": "CVE-2026-1042 (CVSS 9.8) actively exploited per CISA KEV"
},
"security_rating": {
"score": 35,
"grade": "C+",
"tls_valid": true,
"spf_pass": true,
"dmarc_policy": "quarantine",
"open_ports": 4
},
"incident_history": {
"score": 39,
"breach_count": 2,
"last_breach": "2025-08-14",
"dark_web_mentions": 12,
"credential_leaks": 340
},
"operational_health": {
"score": 20,
"uptime_30d": 99.7,
"cloud_provider": "AWS",
"redundancy_regions": 2,
"status_page_incidents_30d": 3
},
"compliance_posture": {
"score": 45,
"certifications": ["SOC 2 Type II", "ISO 27001"],
"missing_frameworks": ["FedRAMP", "HIPAA BAA"],
"last_audit_date": "2025-11-20"
},
"eol_exposure": {
"score": 35,
"eol_components": 2,
"detail": "PostgreSQL 12.0 EOL 2024-11-14, jQuery 2.x EOL 2023-01-01"
}
},
"narrative": "CloudCorp SaaS presents MEDIUM risk driven primarily by a critical actively-exploited vulnerability (CVE-2026-1042), 2 historical breach events with 340 leaked credentials in circulation, and 2 end-of-life software components lacking security patch coverage. Compensating strengths include valid SOC 2 Type II certification and 99.7% uptime over 30 days.",
"assessed_at": "2026-03-07T14:32:18Z"
}5. The Bottom Line
You just triaged your entire new-vendor pipeline for the quarter in the time it used to take to assess one.
What previously required a team of analysts spending 40–80 hours per vendor—at $3,600–$8,000 each—now executes as a single API call returning a 6-dimension risk profile in under 2 seconds. Multiply that across 200 vendors and the math is unambiguous: ComplianceHarbor replaces $720,000–$1.6M in annual manual assessment costs with continuous, real-time vendor risk intelligence.
But cost savings are the secondary benefit. The primary value is visibility. Manual assessments are point-in-time snapshots that begin degrading the moment the questionnaire is filed. ComplianceHarbor’s 48 MCP tools provide continuous vendor risk intelligence—when a vendor’s security posture changes, when new CVEs hit their stack, when their credentials appear on dark web markets, your risk profile updates automatically. Internal Control Connectors add bidirectional context by cross-referencing your own identity, endpoint, and ticketing posture against vendor access patterns. And the Remediation Workflow Engine ensures that high-risk vendor findings are tracked through resolution with SHA-256 evidence receipts—not buried in spreadsheets.
For the VP of Vendor Risk facing federal SBOM mandates, NIS2 supply chain requirements, and a board that expects defensible third-party risk posture: this is not an efficiency upgrade. It is a capability that did not exist before.
Generate a Shareable Vendor Assessment Report
Use the generate_report tool with the vendor_assessment report type to produce a server-rendered vendor risk report. Share the report URL (/report/:requestId), available for 24 hours, with procurement, legal, and third-party risk teams for vendor onboarding and renewal decisions.
Get Started
See all 6 risk dimensions scored in real time against your own vendor scenarios.
Start Free TrialReady to get started with VendorRisk?
See pricing →