From Detection to Action in 2 Seconds: How CISOs Close the Loop on Active Threats
Table of Contents
In 2024 alone, over 28,000 CVEs were published—a record-breaking flood of vulnerability disclosures that no human team can manually triage. For CISOs, the challenge is no longer finding vulnerabilities; it’s distinguishing which ones are actively being weaponized against their specific technology stack, and closing the gap between detection and operational response before threat actors exploit the window. This walkthrough shows how ComplianceHarbor collapses the detection-to-action cycle from days to seconds, automatically connecting threat intelligence to CI/CD pipeline decisions with auditable evidence at every step.
1. The Business Problem
Security teams are drowning in CVE noise. With 28,000+ CVEs published in 2024, the raw volume of vulnerability disclosures has outpaced every manual triage process ever designed. SOC analysts spend hours each day cross-referencing CISA’s Known Exploited Vulnerabilities catalog, the National Vulnerability Database, and commercial threat feeds—trying to answer one deceptively simple question: is this CVE actually being exploited against our stack right now?
The answer matters because the gap between vulnerability detection and operational response is where breaches happen. The average time from CVE publication to first exploitation is 15 days for broadly targeted vulnerabilities, but for high-profile targets—healthcare, financial services, critical infrastructure—weaponization often happens within hours. Meanwhile, engineering teams continue deploying changes during active exploitation windows because the intelligence never reaches the CI/CD pipeline. The security team knows about the threat. The engineering team doesn’t. And the deployment proceeds.
The consequences are well documented. IBM’s 2024 Cost of a Data Breach Report puts the average dwell time—the period between initial compromise and detection—at 204 days. ITIC’s 2024 Hourly Cost of Downtime Survey reports that large enterprises lose an average of $9,000 per minute during unplanned outages. For a healthcare organization, where the average breach cost reaches $10.93M, the financial exposure from a single missed exploitation window can exceed the entire annual security budget.
The root cause is architectural: vulnerability intelligence and deployment operations exist in separate systems, managed by separate teams, on separate timelines. ComplianceHarbor eliminates that gap by creating a closed-loop pipeline that connects real-time threat intelligence directly to CI/CD deployment gates—automatically, with no analyst intervention required.
2. The Demo Walkthrough
Meet Sarah Chen, CISO at a mid-market healthcare organization with 4,000 employees running a hybrid cloud environment on AWS and Azure. Her technology stack includes Exchange Server 2019, PostgreSQL 15, and Node.js 20. It’s March 2026, and her team is about to see ComplianceHarbor’s threat intelligence pipeline in action.
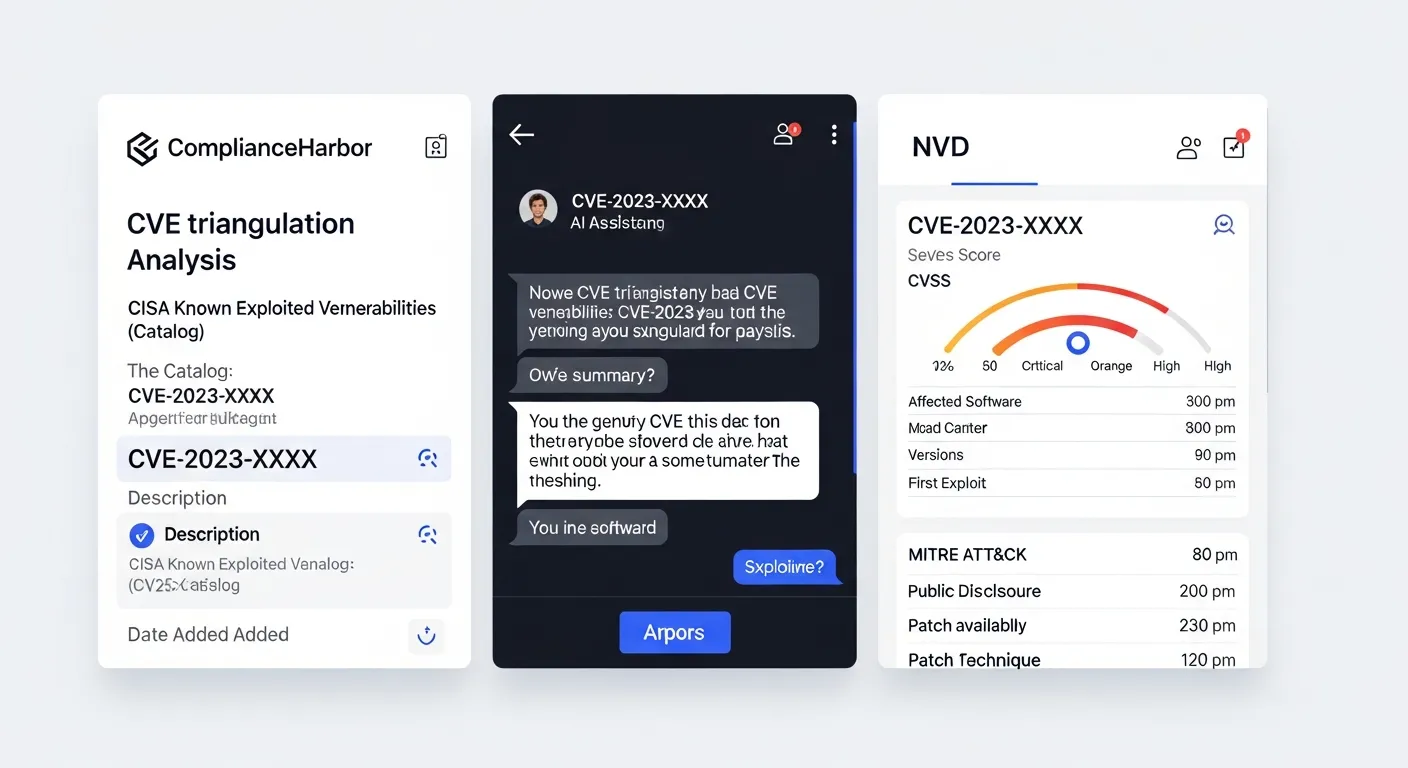
Step 1: CVE Detection and Cross-Referencing
ComplianceHarbor’s automated scan detects CVE-2024-21413 in the NVD bulk feed—a critical Microsoft Outlook Remote Code Execution vulnerability with a CVSS base score of 9.8. Within seconds, the platform cross-references this CVE against two additional authoritative sources. CISA’s Known Exploited Vulnerabilities catalog confirms the vulnerability is actively exploited in the wild. AlienVault OTX pulse data reveals active campaigns specifically targeting the healthcare sector using this CVE as an initial access vector.
Step 2: CVE Triangulation and Severity Escalation
CVE triangulation fires. Because CVE-2024-21413 appears in all three authoritative sources—NVD, CISA KEV, and AlienVault OTX—and it targets a technology in Sarah’s stack (Exchange Server 2019), the platform automatically escalates severity from the base CVSS score to CRITICAL with an “active exploitation confirmed” flag. This is not a theoretical vulnerability sitting in a database. It is a confirmed, weaponized threat targeting her industry and her infrastructure.
Step 3: FAIR-Aligned Financial Re-Quantification
With the severity escalation confirmed, ComplianceHarbor’s FAIR-aligned quantification engine re-calculates financial impact in real time. The healthcare industry multiplier is applied—$10.93M average breach cost from IBM’s 2024 report—and the numbers shift dramatically. The Annualized Loss Expectancy (ALE) jumps from $800K to $2.4M. Value at Risk is recalculated at $3.8M. These are not static figures from a quarterly report; they are live calculations that reflect the threat landscape as it exists right now.
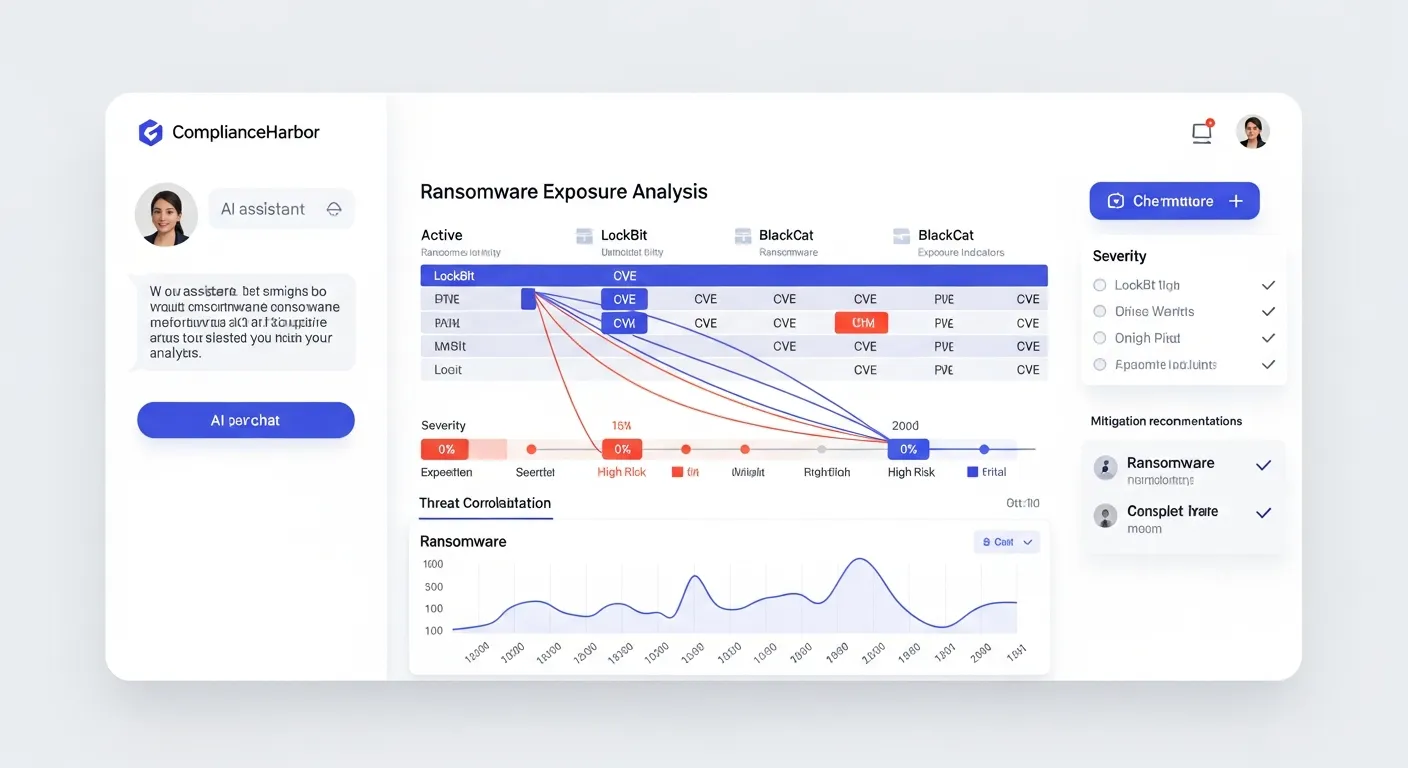
Step 4: Ransomware Exposure Correlation
The ransomware exposure check fires next. ComplianceHarbor cross-references the CVE against known ransomware campaigns and confirms that CVE-2024-21413 is linked to both LockBit and BlackCat campaigns. Three ransomware-linked KEVs now affect the Exchange infrastructure. Dark web intelligence confirms active tooling—exploit kits incorporating CVE-2024-21413 are being traded and deployed by ransomware affiliates targeting healthcare organizations.
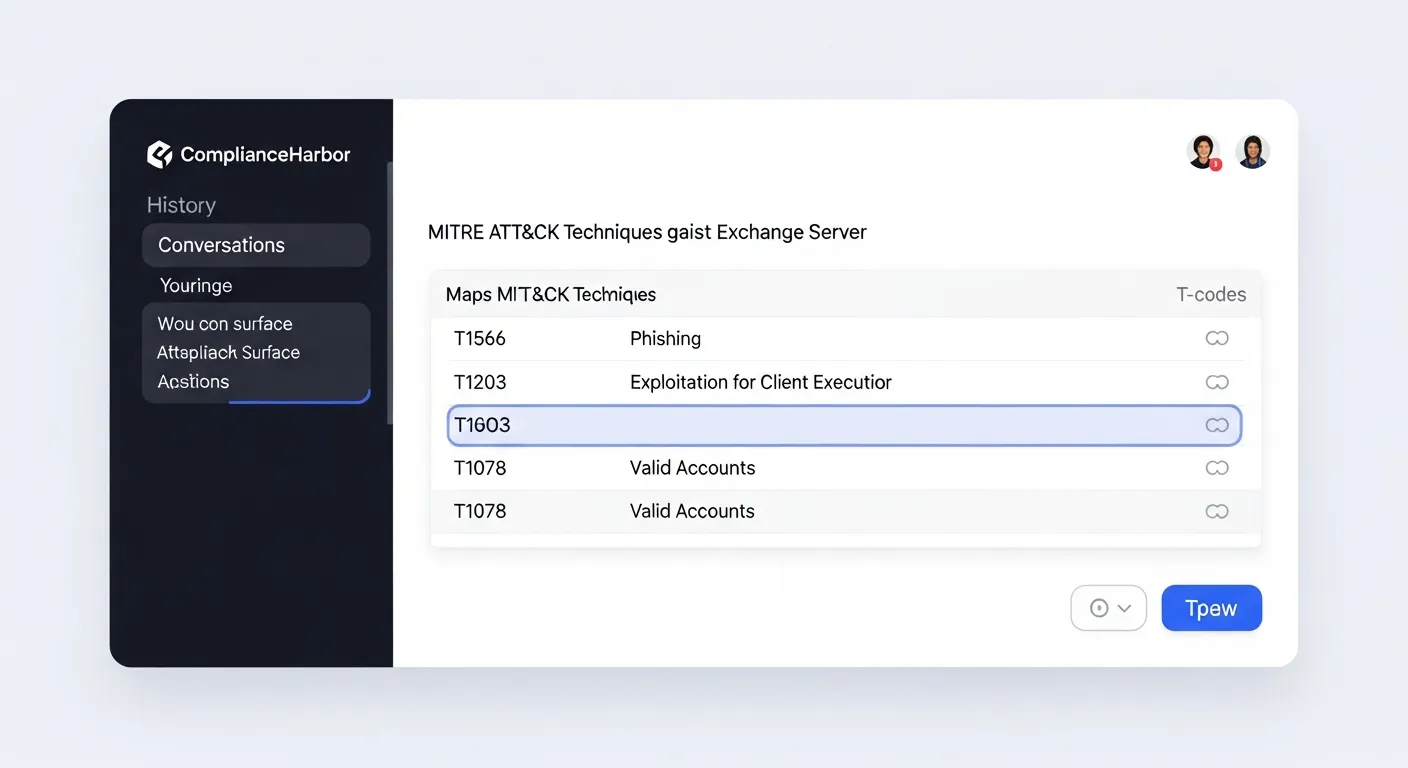
Step 5: MITRE ATT&CK TTP Matching
MITRE ATT&CK TTP matching identifies the complete attack pattern associated with the vulnerability. The platform maps CVE-2024-21413 to three techniques: T1566.001 (Spearphishing Attachment) as the initial access vector, T1203 (Exploitation for Client Execution) as the execution method, and T1078 (Valid Accounts) for persistence and lateral movement. Attack surface mapping reveals 4 exposed techniques across the Exchange deployment, giving Sarah’s team a precise map of how an attacker would move through their infrastructure.
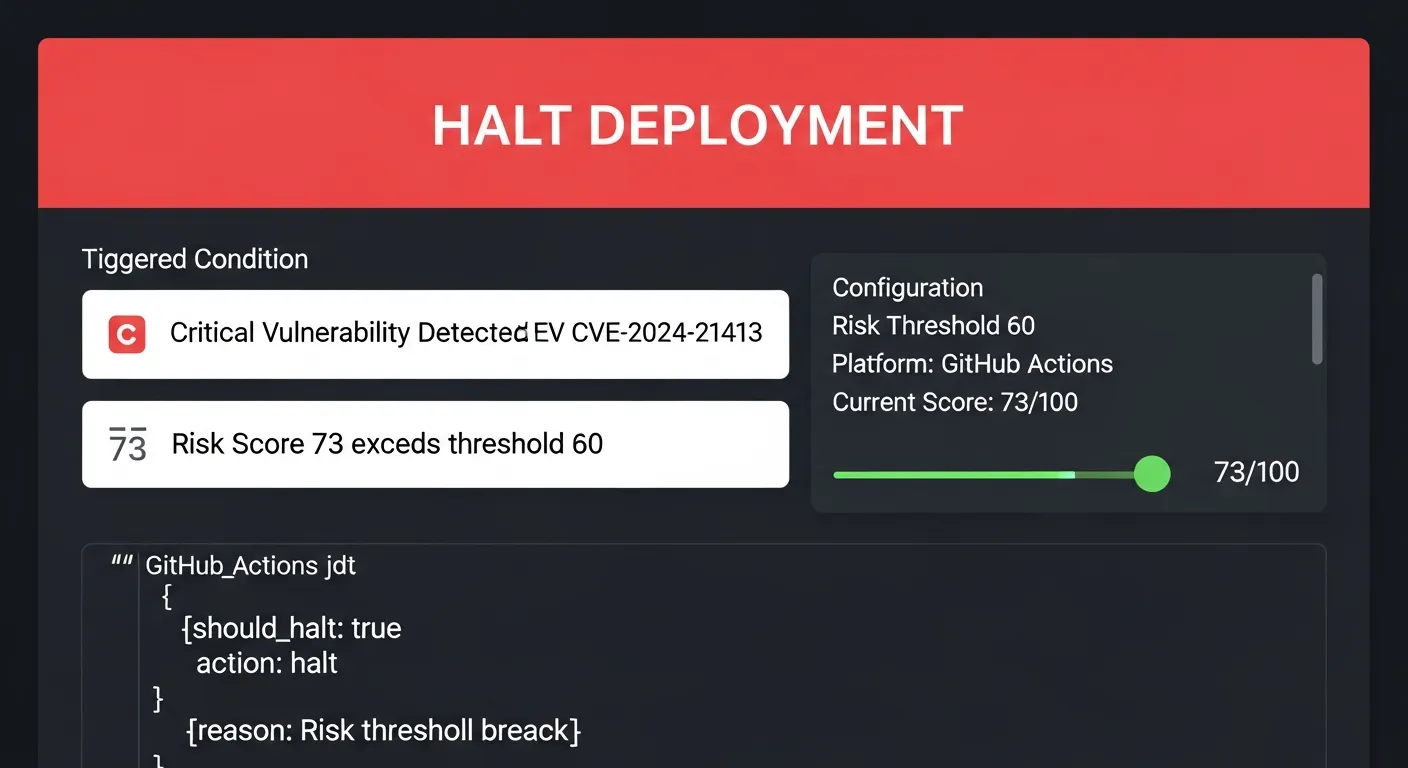
Step 6: Automated CI/CD Pipeline Halt
Here is where the loop closes. A deployment for “Exchange Server cumulative update” is scheduled for tonight. ComplianceHarbor’s deployment gate evaluates the change against the current threat landscape and calculates a risk score of 78/100. Three halt triggers fire: critical vulnerability actively exploited, ransomware campaign targeting the technology stack, and unresolved KEV remediation deadline. The CI/CD pipeline receives an automatic HALT payload formatted for GitHub Actions. The deployment is blocked before it reaches production—no analyst intervention, no manual ticket, no emergency Slack thread.
Step 7: Alternative Window Recommendations
Halting a deployment is only half the answer. ComplianceHarbor immediately suggests alternative windows based on projected threat conditions and remediation timelines. Tuesday, March 10 scores 31/100—after Patch Tuesday patches are available and the most critical KEV remediation is expected to be complete. Wednesday, March 12 scores 28/100—the optimal window with full KEV remediation, patch application, and reduced threat activity. Sarah’s team knows exactly when to reschedule and what remediation items to complete before proceeding.
Key Insight
The entire detection-to-action chain—from NVD publication to CI/CD pipeline halt—happened automatically. No analyst intervention. No manual ticket creation. No waiting for the weekly vulnerability review meeting.
3. Tools Included in ThreatSight
The demo walkthrough exercises six core capabilities that form ComplianceHarbor’s closed-loop threat intelligence pipeline:
CVE Triangulation
Cross-references CISA KEV, NIST NVD, MITRE CVE 5.0, and AlienVault OTX to confirm active exploitation. Only CVEs that appear across multiple authoritative sources AND match your technology stack trigger escalation.
Ransomware Exposure Correlation
Cross-references KEV entries with dark web intelligence and OTX threat feeds to identify CVEs actively weaponized by ransomware groups. Maps to specific campaigns (LockBit, BlackCat, Cl0p, etc.).
MITRE ATT&CK TTP Matching
Maps detected vulnerabilities to MITRE ATT&CK techniques, tactics, and procedures. Identifies which attack patterns are viable against your infrastructure and quantifies the attack surface.
Attack Surface Mapping
Combines NVD vulnerability data with MITRE ATT&CK intelligence to map your exposed attack surface. Identifies which techniques have viable exploit paths through your technology stack.
Automated CI/CD Rollback Triggers
When risk thresholds are exceeded, generates platform-specific halt payloads for GitHub Actions, Jenkins, or GitLab CI. Prevents risky deployments during active threat campaigns without manual intervention.
FAIR-Aligned Re-Quantification
Financial impact is continuously recalculated as threat intelligence changes. When a CVE moves from “published” to “actively exploited in your industry,” the ALE, SLE, and VaR figures update automatically with industry-specific cost multipliers.
Remediation Workflow Engine
Automatically creates tracked remediation findings from threat detections. Each finding follows a full lifecycle (open → in_progress → resolved/accepted) with SHA-256 evidence receipts and ALE trend tracking for financial impact over time.
Internal Control Connectors
Ingests real-time signals from endpoint management (CrowdStrike, Defender), identity providers (Okta, Azure AD), and ticketing systems (ServiceNow, Jira) to enrich threat context with actual control posture data.
Board Deck Reporting
Generates executive-ready board deck reports combining risk posture, FAIR-aligned CRQ financials, compliance status, and prioritized recommendations—ready for board presentation without manual assembly.
4. Automated Remediation Workflow
Detection without remediation is just awareness. When ComplianceHarbor halts a deployment or detects an actively exploited vulnerability, the platform doesn’t stop at alerting—it automatically creates tracked remediation findings that ensure every threat is driven to resolution.
Step 8: Auto-Creating Remediation Findings
When the CI/CD pipeline halt fires for CVE-2024-21413, ComplianceHarbor’s Remediation Workflow Engine automatically creates a remediation finding linked to the assessment. The finding captures the full threat context: the CVE identifier, the CVSS score, the ransomware campaign correlation, the MITRE ATT&CK techniques, and the FAIR-aligned financial exposure. Sarah’s team doesn’t need to manually create a ticket or copy-paste assessment data into a tracking system—the finding is created with complete context the moment the threat is detected.
Each finding follows a structured lifecycle: open when created, in_progress when an engineer is actively working on remediation, and resolved or accepted when the vulnerability is patched or the risk is formally accepted. Every state transition generates a SHA-256 hashed evidence receipt—creating a cryptographically verifiable audit trail that maps directly to SOC 2, ISO 27001, and NIST CSF controls.
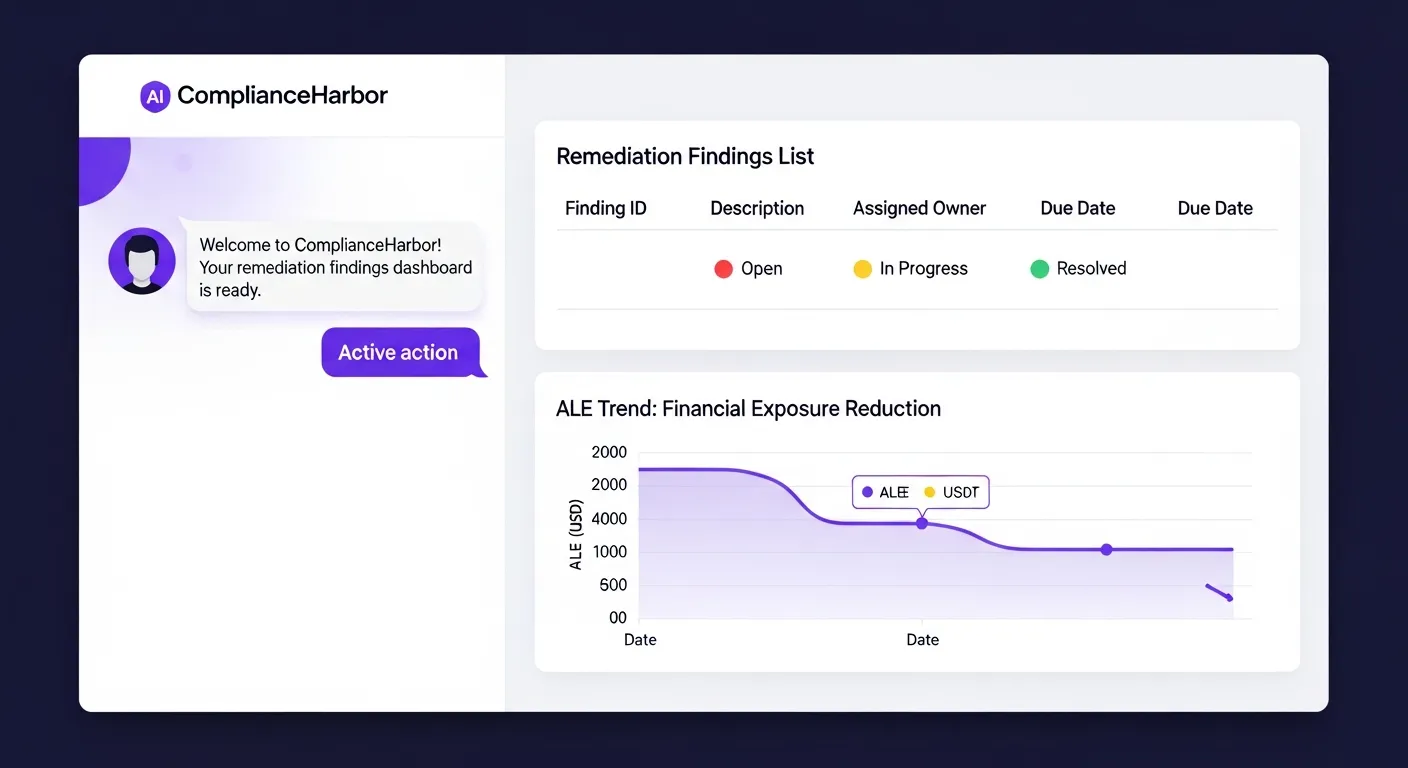
Step 9: ALE Trend Tracking
As Sarah’s team works through the remediation findings, the Annualized Loss Expectancy trend updates in real time. The ALE for the Exchange Server exposure started at $2.4M when the active exploitation was confirmed. After the first patch is applied and the KEV finding is resolved, the ALE drops to $1.1M. After the remaining ransomware-linked findings are addressed, it drops further to $340K. The CISO can show the board exactly how remediation investment translates to financial risk reduction—not in vague qualitative terms, but in precise dollar figures tracked over time.
5. Internal Control Connector Signals
Threat intelligence is only half the picture. To truly assess whether a vulnerability is exploitable in your environment, you need to know your actual control posture. ComplianceHarbor’s Internal Control Connectors ingest real-time signals from your existing security tools to enrich every threat assessment with ground-truth data about your defenses.
Endpoint Signals: EDR Coverage as Threat Context
When evaluating CVE-2024-21413 against Sarah’s Exchange infrastructure, ComplianceHarbor pulls real-time endpoint signals from her CrowdStrike deployment. The platform confirms that 96% EDR coverage is maintained across the Exchange server fleet, with patch compliance at 87%. These signals directly inform the risk calculation—a 96% EDR coverage rate means the T1203 (Exploitation for Client Execution) attack technique is partially mitigated by behavioral detection, reducing the effective probability of exploitation. Without these signals, the platform would have to assume worst-case control posture, inflating the risk score unnecessarily.
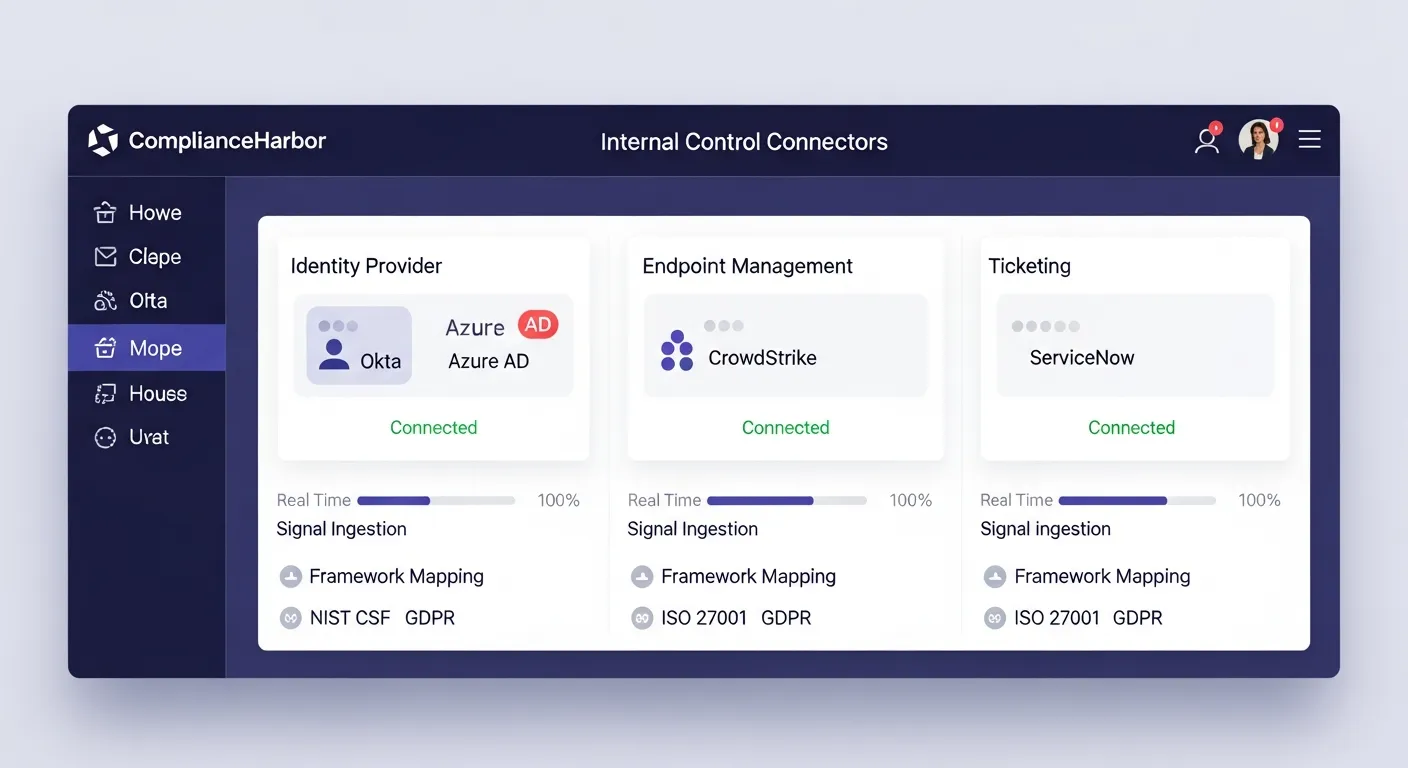
Identity Signals: Access Control Validation
The identity connector pulls MFA enrollment rates and access review status from Sarah’s Okta deployment. With 94% MFA enrollment across the organization, the T1078 (Valid Accounts) attack technique identified by MITRE ATT&CK mapping becomes significantly harder to execute—even if an attacker obtains credentials via spearphishing, MFA provides a second barrier. These signals map directly to SOC 2 CC6.1 and NIST CSF PR.AC-1 controls, providing evidence that access controls are functioning as designed.
Closed-Loop Evidence
Control connector signals automatically flow into evidence generation. When Sarah’s team generates compliance evidence for their SOC 2 audit, the identity and endpoint signals are included as real-time control attestation—no manual screenshot collection required.
6. How It Works: The Intelligence Pipeline
ComplianceHarbor’s intelligence pipeline transforms raw threat data into operational decisions through eight stages:
- 26 data sources refresh on staggered schedules—the NVD bulk feed updates every 2 hours, CISA KEV refreshes daily, AlienVault OTX pulses stream continuously, and MITRE ATT&CK data syncs weekly. Each source is independently validated and timestamped to ensure intelligence freshness.
- Deduplication layer prevents thundering herd problems—when multiple assessments request the same data source concurrently, they share a single API call. This eliminates redundant external requests and ensures consistent data across simultaneous evaluations.
- Conflict analyzer evaluates all 26 conflict types against the change context—technology stack, industry vertical, geographic region, and deployment timing. Each conflict is classified by severity and mapped to the specific systems affected.
- Scoring engine applies hyperbolic diminishing returns to prevent score inflation. Ten low-severity conflicts do not outweigh one critical active exploitation. The scoring model ensures that signal integrity is preserved regardless of the volume of contributing factors.
- Deployment gate evaluates configurable thresholds and generates platform-specific CI/CD payloads. Whether your pipeline runs on GitHub Actions, Jenkins, or GitLab CI, the halt payload is formatted for native consumption—no custom parsing required.
- Evidence generator creates SHA-256 hashed audit receipts mapped to SOC 2, ISO 27001, and NIST CSF controls. Every automated decision—every escalation, every halt, every window recommendation—has an independently verifiable, cryptographically signed audit trail.
- Control connectors ingest real-time signals from endpoint management, identity providers, and ticketing systems. EDR coverage, MFA enrollment, and change approval rates are continuously fed into risk calculations, ensuring assessments reflect actual control posture rather than assumed baselines.
- Remediation engine automatically creates tracked findings from threat detections and deployment halts. Each finding follows a full lifecycle with SHA-256 evidence receipts, and ALE trends track the financial impact of remediation progress over time.
7. The Bottom Line
ComplianceHarbor closes the loop that every CISO knows is open: the gap between knowing about a threat and doing something about it. The platform transforms vulnerability intelligence from a passive awareness exercise into an active operational control—one that reaches into the CI/CD pipeline, prevents exploitation before it starts, automatically creates tracked remediation findings, and generates board-ready reports that communicate risk reduction in financial terms.

$9,000/min
Average enterprise downtime cost. One prevented exploitation incident pays for years of the platform.
Source: ITIC 2024
15 days → 2 seconds
From average CVE-to-exploit time to automated detection-to-action. ComplianceHarbor closes the loop before the attack begins.
$10.93M
Average healthcare breach cost. FAIR-aligned quantification makes this number your starting point, not your surprise.
Source: IBM Cost of a Data Breach Report, 2024
For CISOs tired of managing security by spreadsheet, ComplianceHarbor provides the closed-loop intelligence pipeline that connects vulnerability detection directly to operational action—with auditable evidence at every step, automated remediation tracking that drives findings to resolution, and board deck reports that translate security posture into the financial language your board demands. No more hoping the weekly vulnerability meeting catches what the threat actors already found.
See It Live
Schedule a 30-minute executive briefing to see ComplianceHarbor detect, quantify, and respond to active threats in your environment.
Data sources referenced: CISA KEV, NIST NVD, MITRE ATT&CK, AlienVault OTX, IBM Cost of a Data Breach Report 2024, ITIC Hourly Cost of Downtime Survey 2024, FAIR Institute benchmarks.
All figures cited are from publicly available reports and are used for illustrative purposes. Actual risk quantification results depend on your organization’s specific technology stack, industry vertical, and threat landscape. ComplianceHarbor does not guarantee specific financial outcomes.
Ready to get started with ThreatSight?
See pricing →