Your Auditor Called — You’re Already Ready: Automating Multi-Framework Compliance Evidence
Table of Contents
Your SOC 2 auditor sends a request list. Your ISO 27001 surveillance audit is in three weeks. Your PCI-DSS QSA wants evidence of continuous monitoring. And your team is about to spend the next 200+ hours pulling screenshots, exporting logs, and manually mapping controls across four overlapping frameworks. What if every piece of evidence was already generated, cryptographically sealed, and framework-mapped—before the auditor even asked?
1. The Business Problem
Compliance Directors face a compounding crisis. The average enterprise spends 200+ hours per audit cycle on manual evidence collection—pulling change records from ServiceNow, exporting vulnerability scans from Qualys, assembling risk assessments from spreadsheets, and mapping each artifact to the relevant control framework. Multiply that across SOC 2, ISO 27001, PCI-DSS, and SOX, and audit preparation becomes a full-time job for a team of three.
Meanwhile, the business cost of compliance delays is tangible and growing:
- SOC 2 delays block $48K–$90K enterprise deals — procurement teams will not sign contracts without a current SOC 2 Type II report, and every week of audit delay is a week of deferred revenue
- Multi-framework overlap creates redundant work — SOC 2 CC8.1, ISO 27001 A.12.1.2, and PCI-DSS Requirement 6 all require change management evidence, yet most teams collect it three separate times in three separate formats
- Evidence integrity is questioned — auditors increasingly challenge manually assembled evidence packages because they cannot verify that artifacts were not created or modified after the fact
The result: compliance teams are trapped in a cycle of reactive, manual evidence gathering that consumes budget, delays deals, and still produces evidence that auditors question. There has to be a better way.
2. The Demo Walkthrough
Let’s walk through how ComplianceHarbor eliminates manual audit preparation by generating immutable, multi-framework compliance evidence automatically—every time a change risk assessment is performed.
Step 1: Evidence Receipt Generation
Every time ComplianceHarbor assesses a change request, it automatically generates an immutable evidence receipt. This is not a retroactive summary—it is a contemporaneous, cryptographically sealed record of the assessment, generated at the moment the decision is made.
The evidence receipt includes a unique Evidence ID, a SHA-256 integrity hash (ensuring the evidence cannot be tampered with after generation), framework badges showing which compliance frameworks the assessment satisfies, and detailed control mappings linking each assessment to specific control IDs.
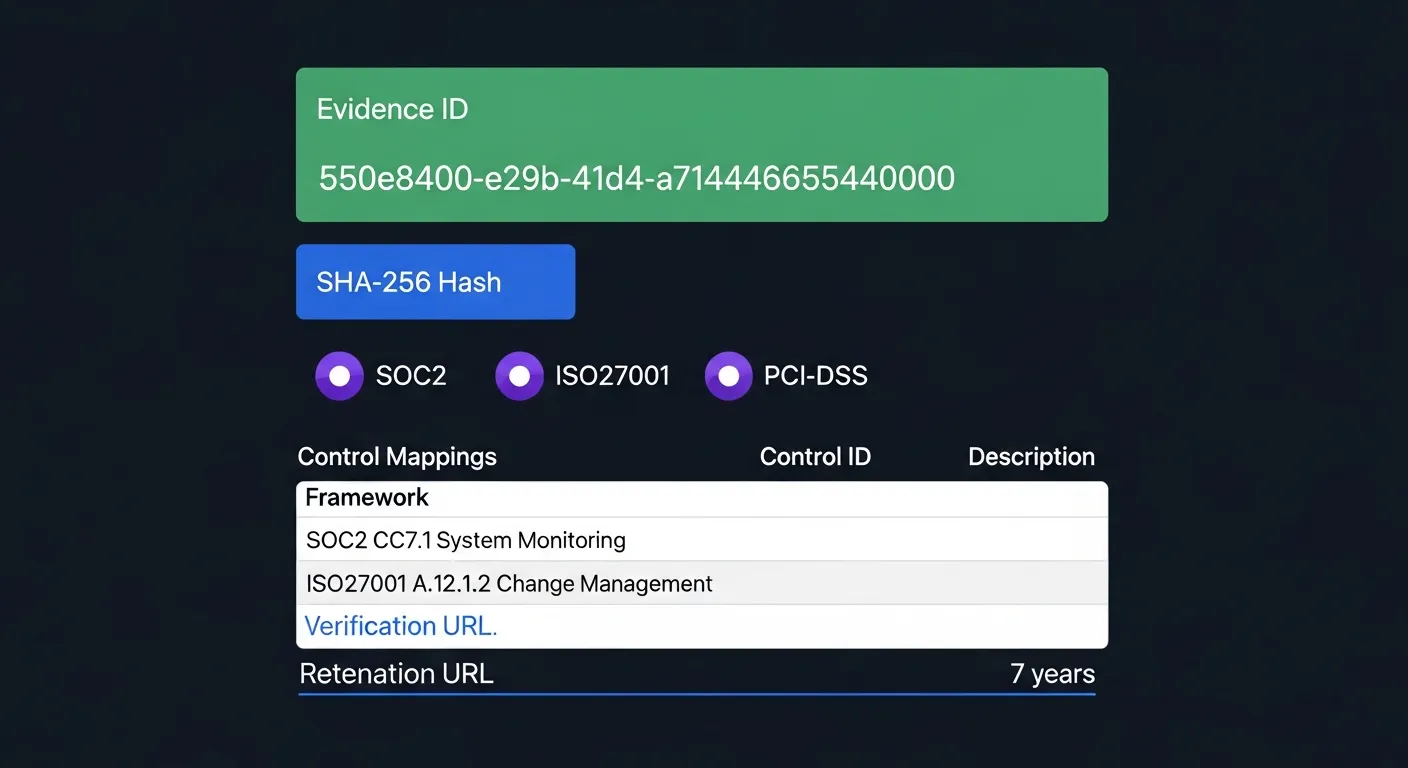
Notice the control mappings table: SOC2 CC7.1 (System Monitoring) and ISO27001 A.12.1.2 (Change Management) are automatically linked to this assessment. The 7-year retention policy ensures evidence is available for any future audit or regulatory inquiry.
Step 2: Compliance Calendar & Regulatory Deadline Tracking
Compliance is not just about generating evidence—it is about generating it at the right time. ComplianceHarbor’s check_compliance_calendar tool provides a unified view of upcoming regulatory deadlines across every framework your organization is subject to.
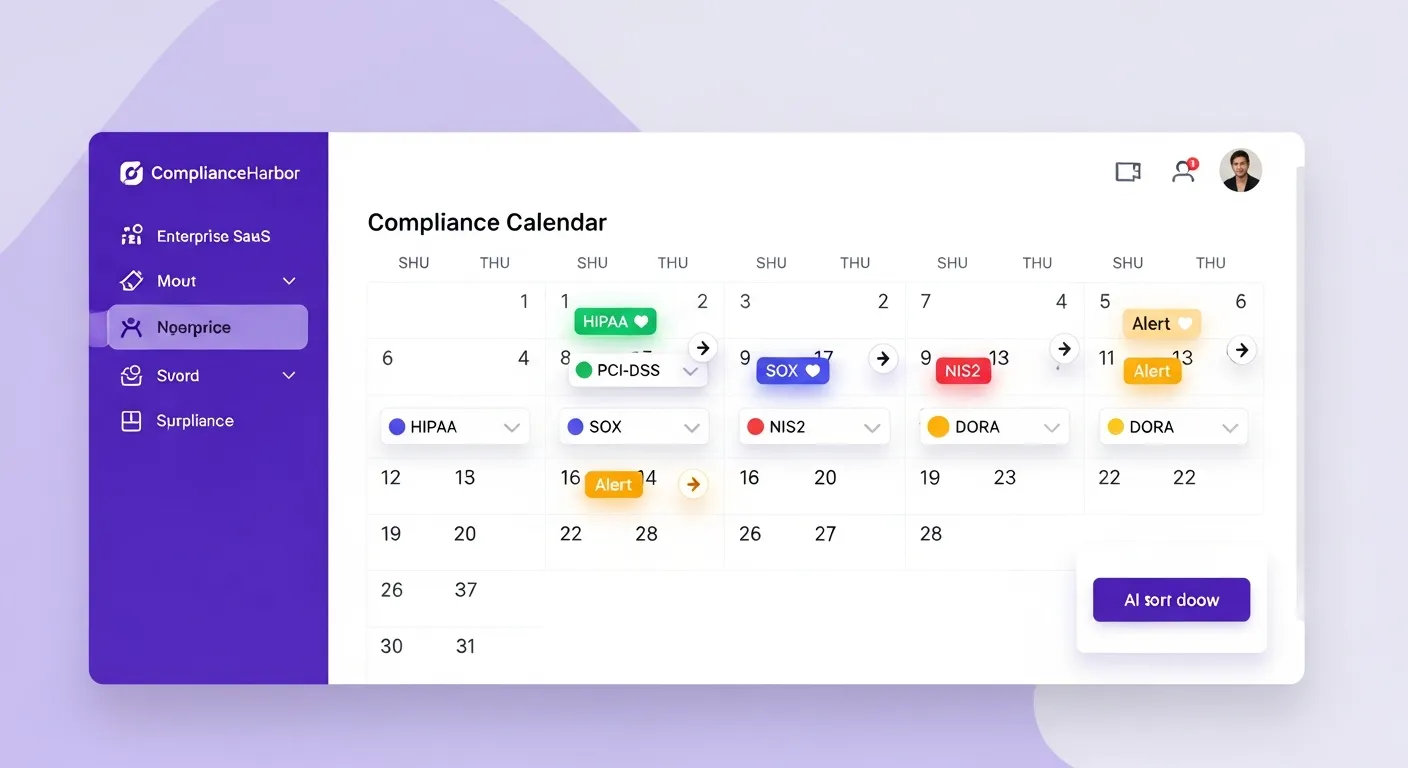
check_compliance_calendar and displaying regulatory deadlines across frameworksThe compliance calendar surfaces critical information that prevents costly violations: SOX freeze periods where no changes should be deployed, PCI-DSS quarterly scan deadlines, HIPAA security assessment windows, NIS2 reporting requirements, and DORA ICT review dates. Each deadline includes a countdown, and the system automatically flags change requests that conflict with upcoming regulatory periods.
The API response includes structured data that integrating systems can use to block deployments during freeze periods or escalate approvals during audit windows:
{
"upcoming_deadlines": [
{
"framework": "SOX",
"event": "Quarter-End Freeze Period",
"date": "2026-03-28",
"days_until_due": 21,
"impact": "No production changes permitted during freeze"
},
{
"framework": "PCI-DSS",
"event": "Quarterly ASV Scan",
"date": "2026-03-31",
"days_until_due": 24,
"impact": "All in-scope systems must pass vulnerability scan"
}
],
"active_freeze_periods": [],
"conflicts_with_proposed_change": true
}Step 3: Continuous Monitoring with Dark Web & Vulnerability Intelligence
Auditors no longer accept point-in-time assessments as sufficient evidence of risk management. Frameworks like SOC 2 (CC7.2) and ISO 27001 (A.12.6.1) require continuous monitoring—evidence that the organization is actively watching for new threats between formal assessment cycles.
ComplianceHarbor’s continuous monitoring capabilities include:
- Dark web exposure checks — monitoring for leaked credentials, breach data, and exploit discussions targeting your organization’s technology stack
- Vulnerability intelligence — real-time tracking of CISA KEV (Known Exploited Vulnerabilities), NVD advisories, and vendor-specific security bulletins
- Vendor security rating monitoring — continuous assessment of third-party security posture across your vendor ecosystem
Every monitoring event generates its own evidence receipt, creating a continuous chain of compliance evidence that auditors can trace from the first day of the audit period to the last.
Step 4: Conflict Detection as Compliance Evidence
When ComplianceHarbor detects conflicts during a change risk assessment, it does not just flag them for operational teams—it captures them as compliance evidence. Each conflict becomes a documented risk decision point with a severity classification, the intelligence source that identified it, and the organizational response.
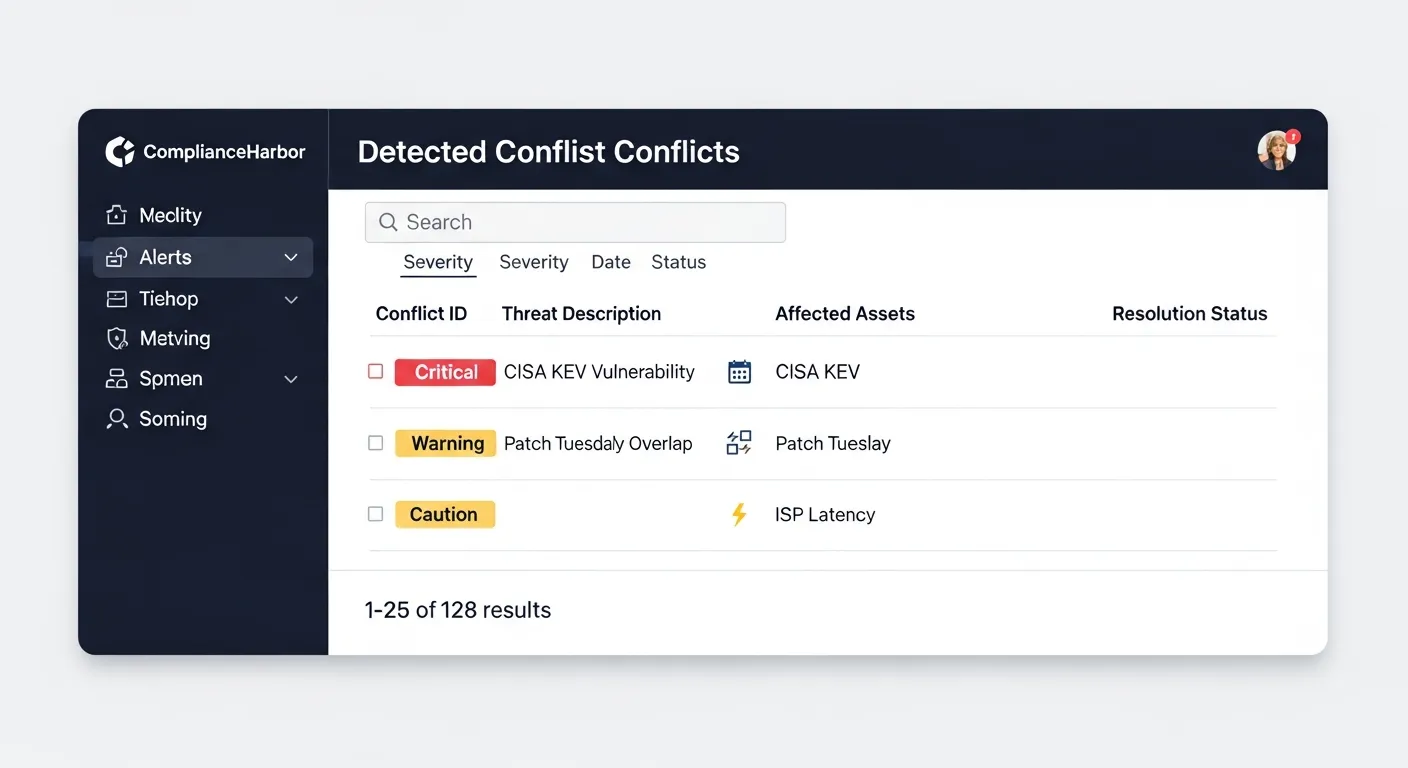
This conflict log serves dual purposes: it informs operational decision-making and it satisfies auditor requirements for documented risk identification and response. SOC 2 CC3.2 (risk identification), ISO 27001 A.12.6.1 (vulnerability management), and PCI-DSS 6.1 (vulnerability identification) all require evidence that the organization systematically identifies and responds to emerging risks.
3. Internal Control Connectors as Evidence Sources
Auditors want proof that your security controls are not just documented—they are actively operating. ComplianceHarbor’s Internal Control Connectors ingest real-time signals from the systems that enforce your controls, transforming operational telemetry into framework-mapped compliance evidence automatically.
Three connector types cover the critical control domains auditors examine:
Identity Provider Connector (Okta / Azure AD)
Ingests identity signals—MFA enrollment rates, access review completion, and privileged account activity—and maps them directly to SOC 2 CC6.1 (Logical and Physical Access Controls) and NIST CSF PR.AC-1 (Identities and Credentials). When your auditor asks “How do you verify that MFA is enforced across your workforce?”, ComplianceHarbor surfaces the live enrollment percentage from your identity provider as cryptographically sealed evidence.
Endpoint Management Connector (CrowdStrike / Defender)
Captures endpoint posture signals—EDR coverage percentages, patch compliance rates, and malware detection metrics—mapping them to NIST CSF DE.CM-08 (Vulnerability Scans) and SOC 2 CC7.1 (Monitoring Activities). Instead of exporting CrowdStrike dashboards into a slide deck, the connector feeds live metrics into every evidence receipt automatically.
Ticketing System Connector (ServiceNow / Jira)
Pulls change approval rates, open priority ticket counts, and SLA compliance data, mapping them to ITIL 4 change management practices and SOC 2 CC8.1 (Change Management). Auditors see a continuous stream of evidence that changes follow an approved workflow—not a manually compiled spreadsheet of change tickets.
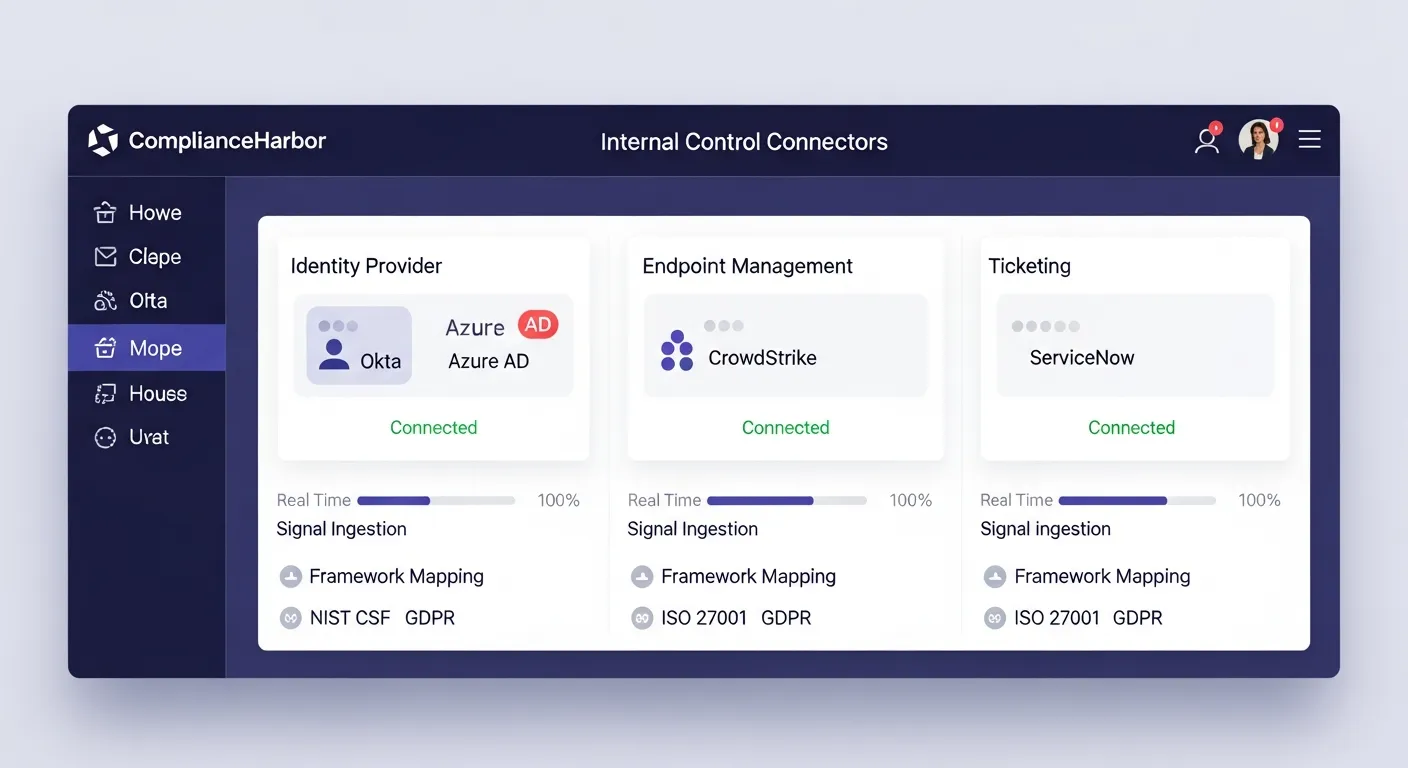
These signals are automatically included in every evidence receipt generated by ComplianceHarbor. When you call generate_evidence_receipt, the response now includes a control_signals section showing the real-time posture from each connected system—giving auditors verifiable proof that your controls were operating at the time of each assessment.
4. Remediation Workflow: The Closed-Loop Audit Trail
Identifying a risk is only half the story auditors want to hear. They also want proof that you acted on it. ComplianceHarbor’s Remediation Workflow Engine creates a closed-loop audit trail: from finding to ticket to resolution to cryptographic evidence—every step documented and immutable.
Finding Creation
When a change risk assessment identifies issues that require follow-up, ComplianceHarbor automatically creates remediation findings. Each finding captures the risk source, severity, affected components, and the Annualized Loss Expectancy (ALE) if the risk remains unaddressed. Findings are created via the create_remediation_findings MCP tool or the POST /api/v1/remediations REST endpoint.
Status Lifecycle
Each finding progresses through a documented lifecycle—open → in_progress → resolved (or accepted if the risk is formally accepted)—with every transition timestamped and attributed. This lifecycle directly satisfies SOC 2 CC7.4 (Response to Identified Vulnerabilities) and ISO 27001 A.16.1.6 (Learning from Information Security Incidents), giving auditors a clear trail from risk identification through remediation.
Resolution with Cryptographic Evidence
When a finding is resolved, ComplianceHarbor generates a SHA-256 evidence receipt sealing the resolution details—who resolved it, when, what action was taken, and the resulting risk reduction in ALE terms. This receipt is tamper-proof and retained for 7 years, ensuring the full finding-to-resolution chain is available for any future audit.
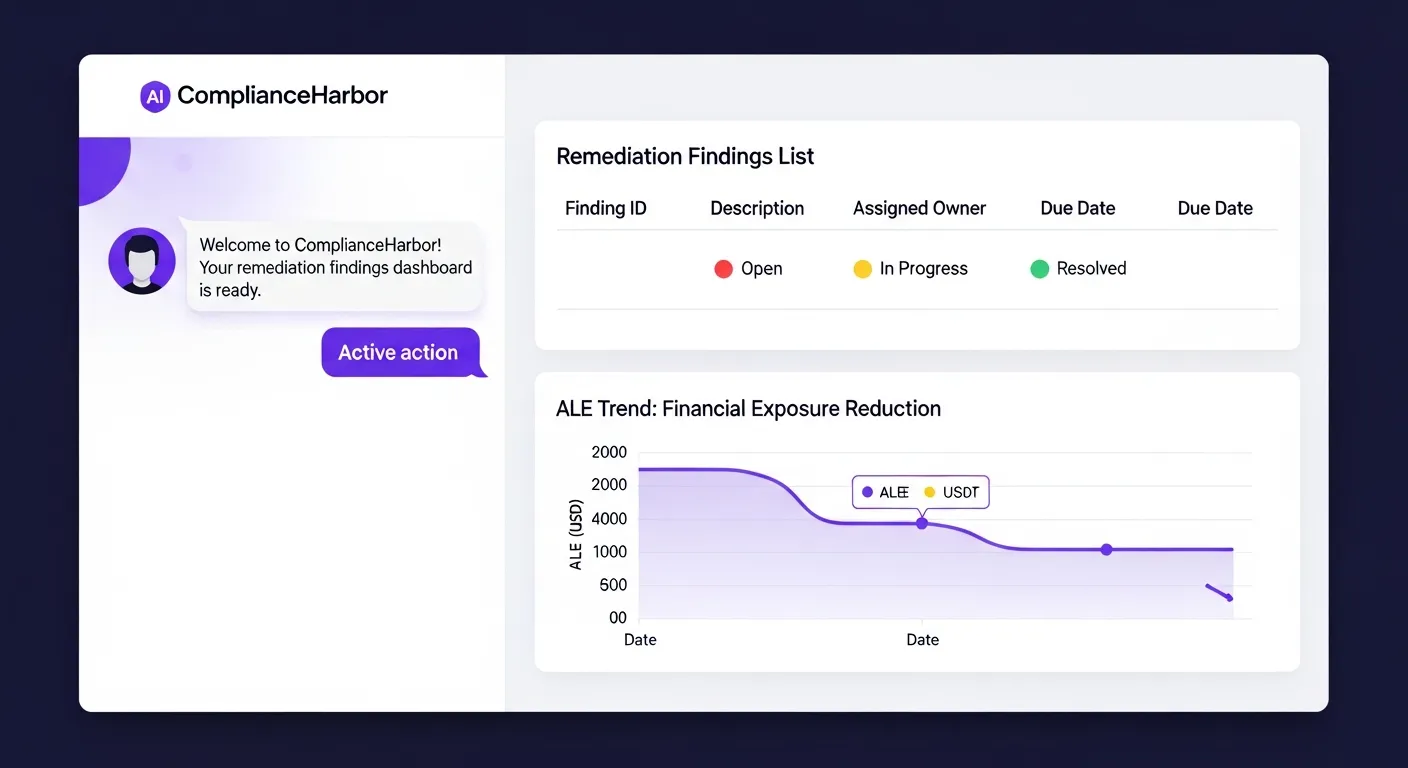
create_remediation_findings and displaying the findings lifecycle with status tracking and ALE trend visualizationThe GET /api/v1/remediations/trend endpoint provides an ALE trend chart that shows how your organization’s aggregate risk exposure has changed over time as findings are resolved. This is the kind of quantified risk reduction data that auditors and board members increasingly demand.
5. Tools Included in AuditReady
The following MCP tools power the compliance evidence automation workflow demonstrated above:
| MCP Tool | What It Returns | Compliance Value |
|---|---|---|
| generate_evidence_receipt | SHA-256 hashed evidence with framework mappings, control IDs, and 7-year retention | Immutable audit trail for every risk decision |
| check_compliance_calendar | Upcoming regulatory deadlines, freeze periods, and audit windows across all frameworks | Prevents freeze period violations and missed deadlines |
| check_dark_web_exposure | Leaked credentials, breach data mentions, and exploit discussions for your technology stack | Continuous monitoring evidence for SOC 2 CC7.2 |
| get_vulnerability_summary | CISA KEV alerts, NVD advisories, and vendor security bulletins with severity ratings | Vulnerability management evidence for PCI-DSS 6.1 |
| assess_change_risk | Composite risk score with conflict detection across 26 intelligence sources | Change management evidence for ISO 27001 A.12.1.2 |
| check_regulatory_pressure | Regulatory velocity metrics, deadline density, filing pressure across agencies | Proactive regulatory change tracking for compliance readiness |
| ingest_identity_signals | MFA enrollment, access reviews, privileged account metrics from Okta/Azure AD | SOC 2 CC6.1 and NIST CSF PR.AC-1 control evidence |
| ingest_endpoint_signals | EDR coverage, patch compliance, malware detection from CrowdStrike/Defender | NIST CSF DE.CM-08 and SOC 2 CC7.1 monitoring evidence |
| ingest_ticketing_signals | Change approval rates, SLA compliance, open priority tickets from ServiceNow/Jira | SOC 2 CC8.1 and ITIL 4 change management evidence |
| create_remediation_findings | Creates tracked findings from assessment results with severity, ALE, and ownership | Documented risk response for SOC 2 CC7.4 |
| resolve_remediation_finding | Closes findings with SHA-256 evidence receipt and resolution details | Closed-loop audit trail from finding to resolution |
6. Sample API Response
The generate_evidence_receipt tool returns a structured evidence payload that integrating systems can store, index, and present to auditors:
{
"evidence_id": "550e8400-e29b-41d4-a714-446655440000",
"evidence_hash": "sha256:a3f2b8c91d4e7f6a0b5c3d2e1f8a9b7c6d5e4f3a2b1c0d9e8f7a6b5c4d3e2f1",
"generated_at": "2026-03-07T14:32:18Z",
"change_request_id": "CHG-2026-0847",
"risk_score": 72,
"risk_label": "High",
"frameworks": ["SOC2", "ISO27001", "PCI-DSS"],
"control_mappings": [
{
"framework": "SOC2",
"control_id": "CC7.1",
"description": "System Monitoring"
},
{
"framework": "SOC2",
"control_id": "CC8.1",
"description": "Change Management"
},
{
"framework": "ISO27001",
"control_id": "A.12.1.2",
"description": "Change Management"
},
{
"framework": "ISO27001",
"control_id": "A.12.6.1",
"description": "Management of Technical Vulnerabilities"
},
{
"framework": "PCI-DSS",
"control_id": "6.1",
"description": "Identify Security Vulnerabilities"
},
{
"framework": "PCI-DSS",
"control_id": "6.4.5",
"description": "Change Control Procedures"
}
],
"conflicts_detected": 6,
"intelligence_sources_evaluated": 26,
"retention_expires_at": "2033-03-07T14:32:18Z",
"verification_url": "/api/v1/evidence/550e8400-e29b-41d4-a714-446655440000/verify"
}Every field in this response is designed for auditability: the evidence_hash ensures tamper detection, the control_mappings array links directly to framework requirements, and the retention_expires_at field confirms the 7-year retention policy required by most regulatory frameworks.
7. The Bottom Line
Every change event automatically generates court-admissible, framework-mapped evidence. Your SOC 2 Type II, ISO 27001 surveillance audit, and PCI-DSS assessment all draw from the same continuously generated, cryptographically verified evidence trail.
With Internal Control Connectors, your identity, endpoint, and ticketing systems feed live operational signals directly into every evidence receipt—proving to auditors that your controls are not just documented but actively enforced. And with the Remediation Workflow Engine, every identified risk follows a tracked lifecycle from finding to resolution, sealed with SHA-256 evidence receipts at each step. The closed loop from finding → ticket → resolution → evidence is exactly the audit trail that SOC 2, ISO 27001, and PCI-DSS assessors demand.
Instead of 200+ hours of manual evidence gathering per audit cycle, your compliance team points auditors to an immutable chain of SHA-256 verified assessments, each mapped to the specific controls it satisfies across every applicable framework. The audit conversation shifts from “Can you prove you assessed this risk?” to “Here is the cryptographic proof of every assessment, every decision, every control mapping, and every remediation—for the entire audit period.”
That is the difference between a compliance program that reacts to auditors and one that is always ready for them.
Generate a Shareable Compliance Evidence Report
Use the generate_report tool with the compliance_evidence report type to produce a server-rendered, shareable compliance report. Each report is available at a shareable URL (/report/:requestId) for 24 hours, giving you time to send it directly to auditors—complete with framework mappings, control IDs, and SHA-256 evidence hashes.
Get Started
Run a live change risk assessment and see the evidence receipt, framework mappings, and compliance calendar in action.
Start Free TrialReady to get started with AuditReady?
See pricing →